
A couple of days ago, North Korea was posed as the fault to the SONY FILMS hack, formally by the FBI. This all followed the major GOP hack on SONY FILMS databases, media, and employees. There is no doubt that the news of and following the SONY FILMS hack is the most breaking and worrisome in both the political and technological industries at the moment. The following article is from BBC News: President Barack Obama has vowed a US response after North Korea’s alleged cyber-attack on Sony Pictures. The US leader also said the studio “made a mistake” in cancelling the Christmas release of The Interview, a satire depicting the assassination of North Korean leader Kim Jong-un. Sony said it still planned to release the film “on a different platform”. On Friday US authorities linked North Korea to the hack, which saw sensitive studio information publicly released. Sony said it cancelled the planned Christmas release of the film after a majority of cinemas refused to show it following anonymous threats. “We will respond,” Mr Obama told reporters on Friday, declining to offer specifics. “We will respond proportionately and in a space, time and manner that we choose.” He added: “We cannot have a society in which some dictator someplace can start imposing censorship in the United States.”

The US leader said it was important to protect both public and private cyber-systems from attack which could have significant economic and social impacts. Mr Obama also noted he believed Sony Pictures was mistaken in failing to go ahead with the release. “Americans cannot change their patterns of behaviour due to the possibility of a terrorist attack,” he said. “That’s not who we are, that’s not what America is about.” Analysis: Dave Lee, BBC technology reporter The FBI say it spotted distinct similarities between the type of malware used in the Sony Pictures attack and code used to attack South Korea last year. Suspicious, yes, but well short of being a smoking gun. When any malware is discovered, it is shared around many experts for analysis – any attacker could simply reversion the code for their own use, like a cover version of a song. But there’s another, better clue: IP addresses – locations, essentially – known to be part of “North Korean infrastructure” formed part of the malware too. This suggests the attack may have been controlled by people who have acted for North Korea in the past. What is the FBI evidence? Sony Pictures chief executive and chairman Michael Lynton later told CNN it had not made an error in pulling the film. He said the president, press and public were mistaken about the withdrawal, saying the decision had only been taken after major chains had refused to screen it. He said: “We have not caved, we have not given in, we have persevered and we have not backed down.” A Sony statement on Friday said that the firm was “actively surveying alternatives to enable us to release the movie on a different platform”. “It is still our hope that anyone who wants to see this movie will get the opportunity to do so,” the statement said. Earlier on Friday, the US Federal Bureau of Investigation officially tied North Korea to the cyber-attack, linking the country to malware used in the incident. Hackers had earlier issued a warning referring to the 11 September 2001 terror attacks, saying “the world will be full of fear” if the film was screened. 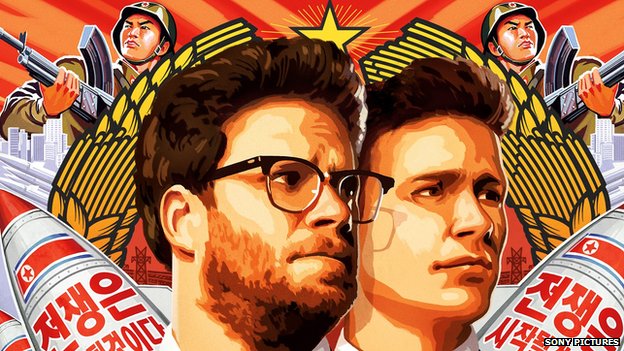 The duo play journalists enlisted to kill Kim Jong-un The movie features James Franco and Seth Rogen as two journalists who are granted an audience with North Korean leader Kim Jong-un. The CIA then enlists the pair to assassinate him. The film was due to have been released over Christmas. The film’s cancelled release drew criticism in Hollywood, with some calling it an attack on the freedom of expression. Actor George Clooney told the trade website Deadline on Thursday the film should be released online, saying Hollywood shouldn’t be threatened by North Korea. In November, a cyber-attack crippled computers at Sony and led to upcoming films and workers’ personal data being leaked online. The hackers also released salary details and social security numbers for thousands of Sony employees – including celebrities.
The duo play journalists enlisted to kill Kim Jong-un The movie features James Franco and Seth Rogen as two journalists who are granted an audience with North Korean leader Kim Jong-un. The CIA then enlists the pair to assassinate him. The film was due to have been released over Christmas. The film’s cancelled release drew criticism in Hollywood, with some calling it an attack on the freedom of expression. Actor George Clooney told the trade website Deadline on Thursday the film should be released online, saying Hollywood shouldn’t be threatened by North Korea. In November, a cyber-attack crippled computers at Sony and led to upcoming films and workers’ personal data being leaked online. The hackers also released salary details and social security numbers for thousands of Sony employees – including celebrities.  North Korea says the film hurts the “dignity of its supreme leadership” North Korea earlier this month denied involvement in the hack – but praised the attack itself as a “righteous deed”. An article on North Korea’s state-run KCNA news agency, quoting the country’s top military body, said suggestions that Pyongyang was behind the attack were “wild rumour”. However, it warned the US that “there are a great number of supporters and sympathisers” of North Korea “all over the world” who may have carried out the attack. In the article, Sony Pictures was accused of “abetting a terrorist act” and “hurting the dignity of the supreme leadership” of North Korea by producing the movie. source: BBC news
North Korea says the film hurts the “dignity of its supreme leadership” North Korea earlier this month denied involvement in the hack – but praised the attack itself as a “righteous deed”. An article on North Korea’s state-run KCNA news agency, quoting the country’s top military body, said suggestions that Pyongyang was behind the attack were “wild rumour”. However, it warned the US that “there are a great number of supporters and sympathisers” of North Korea “all over the world” who may have carried out the attack. In the article, Sony Pictures was accused of “abetting a terrorist act” and “hurting the dignity of the supreme leadership” of North Korea by producing the movie. source: BBC news