To the uninformed, ethical hacking is a criminal practice criminal minds use to tap the data of innocent people. Though it may have some truth in it, Ethical hacking has played a huge role in the world of cybersecurity today. It has helped firms fortify their security and also helped government official gain access to fortified criminal data. In this article, we explore a list of best tools for ethical hacking. These tools are listed below:
1. NMAP

Popular amongst infosec professionals, Nmap (Network Mapper) is an open source security tool that is used by infosec professionals to manage and audit network and operating system security for both local and remote hosts. Despite being more than twenty years, NMAP has constantly been updated. These updates have made NAMP remain relevant in the ethical hack business.
NMAP helps professionals Audit device security, helps detect open ports on remote hosts, helps network mapping and enumeration. NMAP helps find vulnerabilities inside any network, it helps professionals launch massive DNS queries against domains and subdomains. NMAP is supported on MAC OS X, Linux OpenBSD, and Solaris and Microsoft Windows
2. Metasploit

Metasploit is an open source cyber-security tool, that is used as a penetration testing tool to discover remote software vulnerabilities. It is also used as an exploit module development platform.
Metasploit features a framework developed using Ruby. This framework can be used to develop, test and execute exploits easily. The Metasploit framework features a set of security tools that can be used to evade detection system, run security vulnerability scans, execute remote attacks, enumerate networks and hosts. Metasploit is available on Windows, Mac OS X, and Linux
3. Burp Suit
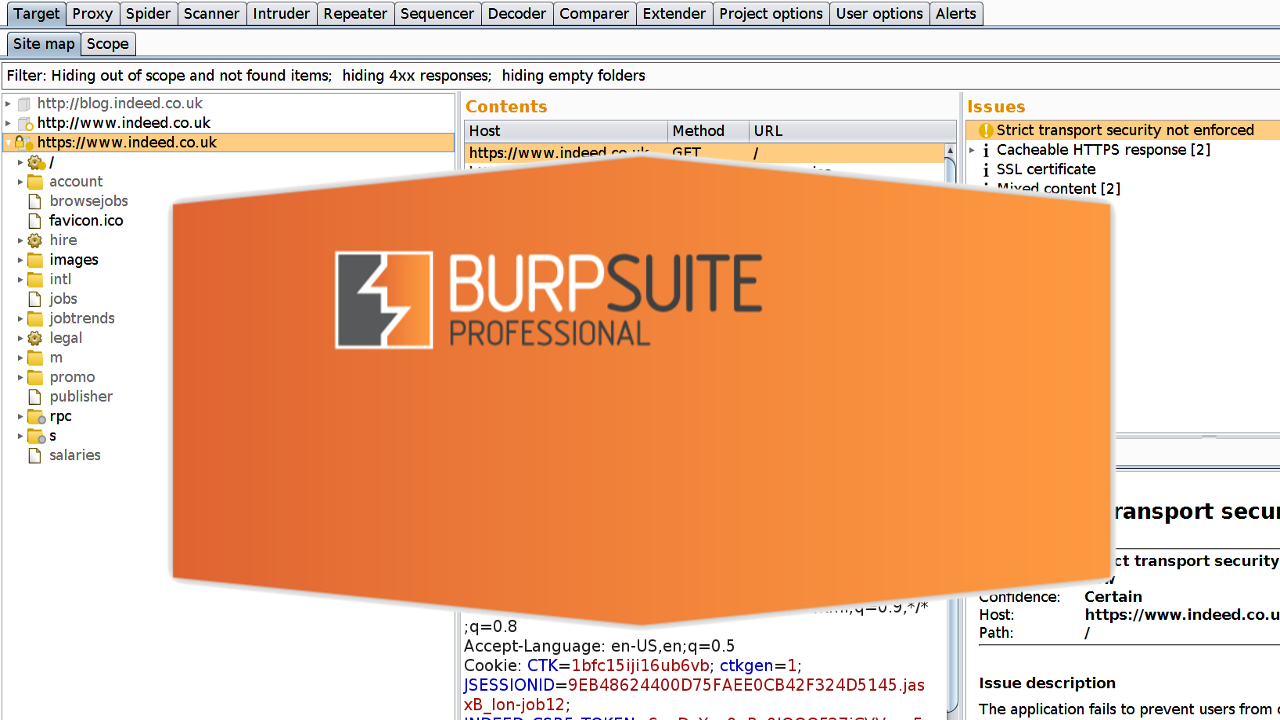
Burp Suite is a tool used in performing security testing of web applications. It houses tools, that work in collaboration to support the entire testing process, om initial mapping and analysis of an application’s attack surface, through to finding and exploiting security vulnerabilities.
Burp suit offers an easy to use interface, giving the administrator full control to combine advanced manual techniques with automation for efficient testing. Burp settings allow for easy configuration. It houses features designed to help users with their work, assistance that aids both the beginner and the professional.
4. Wire Shark
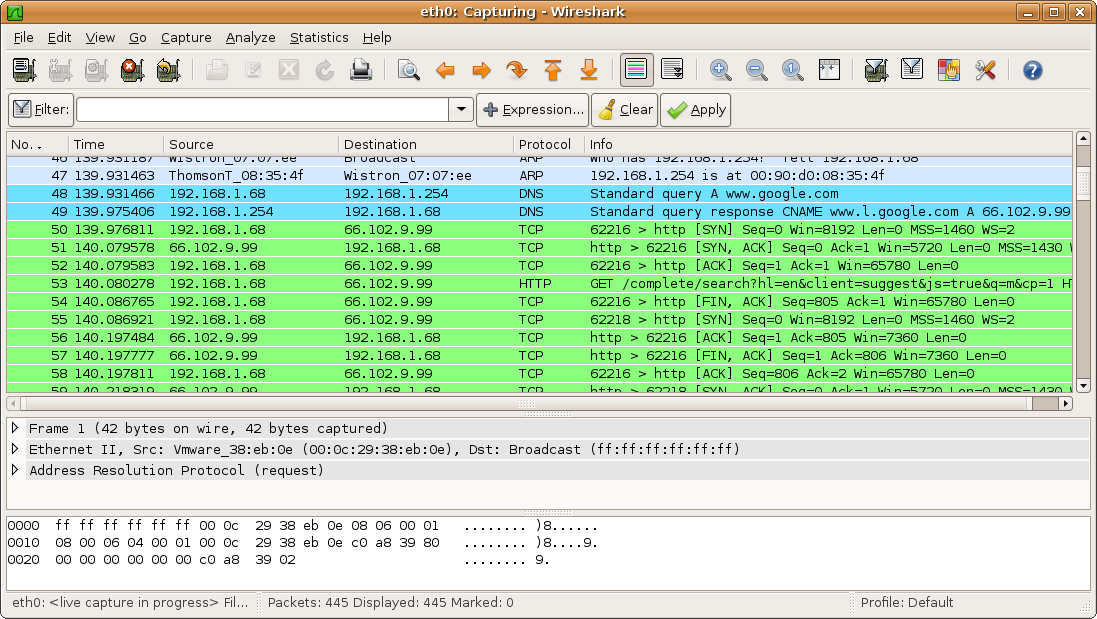
Wire shark is yet another open-source software that can be used to analyze network traffic seamlessly. Wire Shark is popular for its ability to detect security problems in any network, as well as its effectiveness in solving general networking problems.
Wire Shark allows users to intercept and read results in human-readable format while sniffing the network. This makes it easy to identify potential problems, threats, and vulnerabilities.
Wire Shark saves analysis for offline inspection, it features a packet browser, powerful GUI, Rich VoIP analysis. Wireshark Inspects and decompresses gzip files, exports results to XML, PostScript, CSV, or plain text and lots more.
5. Open AVS

Popularly referred to as Nessus, OpenVAS is an open source network scanner that is used by professionals to detect remote vulnerabilities in any host. OpenVAS is famous for its ability to scan network vulnerability.
OpenVAS features a powerful web-based interface, over 50,000 network vulnerability tests, simultaneous multiple host scanning. OpenVAS has the ability to stop, pause and resume scan tasks. OpenVAS features a very powerful CLI available. OpenVAS is fully integrated with Nagios monitoring software.
6. IronWASP

Still, on the topic of best tools for ethical hacking, IronWASP is yet another awesome hacking tool, designed for professionals. IronWASP is a free and multi-platform tool, that makes ethical hacking fun.
IronWASP offers a very intuitive GUI, designed for both the expert and the beginner. It lets users perform full scans from a few clicks. IronWASP features web scan sequence recording, exports results into HTML and RTL format. IronWASL features false positive and negative management. It has full Python and Ruby support for its scripting engine. It is supported on Windows, Linux with Wine, and MacOS using CrossOver
7. Nikto
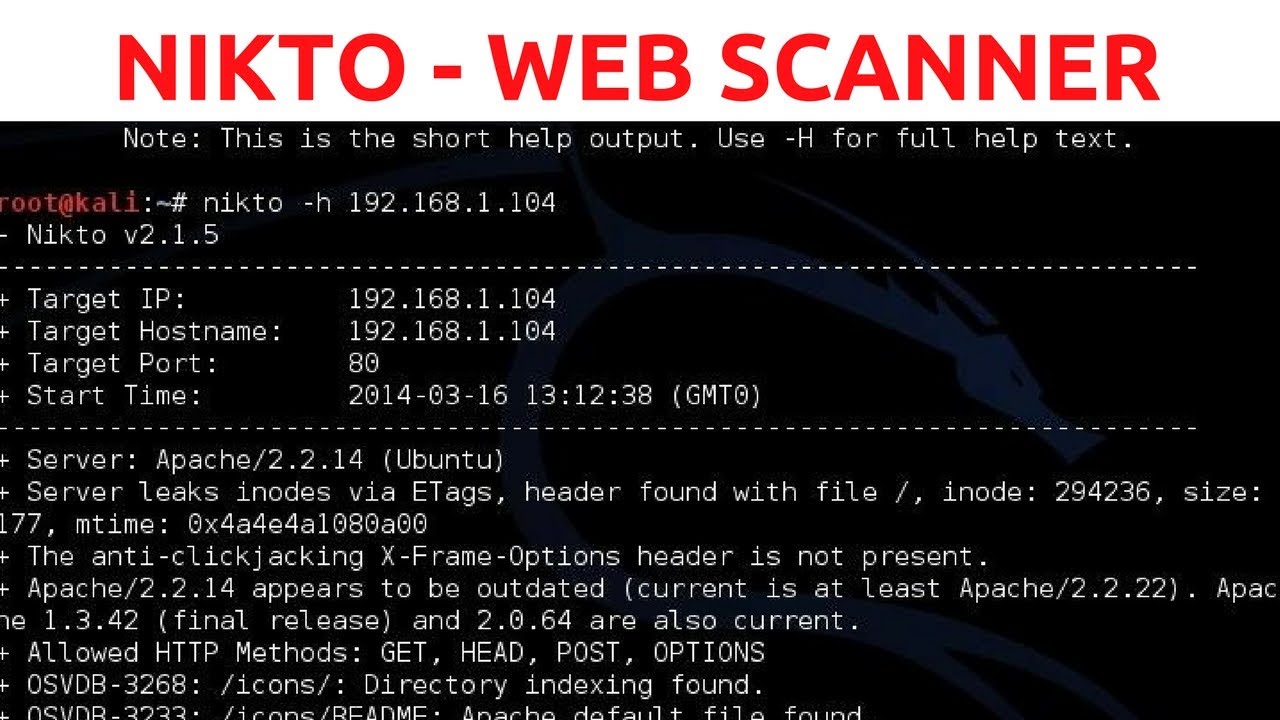
Niko is yet another ethical hacking tool, that is used to scan web serves. It lets users perform a different type of test against the specified remote host. It features a clean and simple command line interfaces, that makes it easy to launch any vulnerability test against your target.
Nikto detects default installation files on any OS, it also detects outdated software applications. Nikto can be used to run XSS vulnerability tests. Nikto can be used to launch dictionary-based brute force attacks. Nikto can be integrated with the Metasploit framework.
8. SQLMap
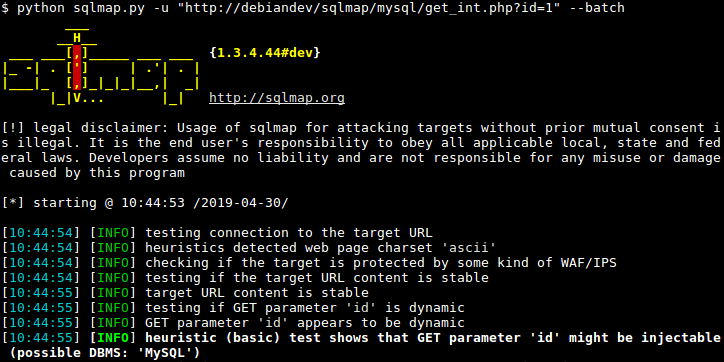
Written in python, SQLMAP is a cybersecurity tool, that helps security researchers launch SQL code injection test against remote hosts. SQLMAP can be used to test different types of SQL based vulnerabilities, helping professionals harden the security of apps and servers.
SQLMAP features a Multiple database server support: Oracle, PostgreSQL, MySQL and MSSQL, MS Access, DB2 or Informix. It has automatic code injection capabilities, password hash recognition, dictionary-based password cracking, user enumeration and lots more.
9. SQL Ninja

SQL Ninja is a vulnerability scanner, that is bundled with Kali Linux distribution. SQL Ninja is a tool used to target and exploit web apps that use MS SQL server as the backend database server.
SQL Ninja can be run in different modes. Examples of such modes include: Test mode, verbose mode, fingerprint remote database mode, brute force attack with a word list, direct shell & reverse shell, canner for outbound ports, reverse ICMP Shell and NS tunnelled shell
10. Wapiti

Last but not least, Wapiti is yet another ethical tool designed for professionals. It open-source command line based vulnerability scanner written in python. It is famous for its ability to find security flaws in many web applications.
Wapiti can be used to detect security holes like XSS attacks, SQL injections, XPath injections, XXE injections, CRLF injections, Server-Side request forgery. Wapiti has the ability to pause and resume scans, it highlights vulnerabilities found inside the terminal, generates reports and export into HTML, XML, JSON, and TXT activates and deactivates multiple attack modules, Removes parameters from certain URLs. Wapiti can be used to bypass SSL certificate verification, URL extractor from javascript, timeout configuration for large scans and lots more.
There you have it – A comprehensive list of the best tools for ethical hacking. If you have other recommendations, feel free to drop them in the comment section below. we would love to hear from you.