Email often straddles a fine line between help and hindrance. It’s an invaluable tool, no doubt about it, but sometimes it can be a stubborn, unwieldy, and intrusive monster—maybe even a security threat.
So who’s in charge around here—you or your inbox? With the right tools, services, and knowledge you can tame the unruly email beast. It’s time to evolve from email user to email power user, and we’ve got just the six tips you need. Start by learning how to add a snooze button to your inbox, then wrangle Gmail to make it smarter and more cooperative. Keep your inbox free of spam with disposable email addresses, then check to make sure your primary addresses haven’t been compromised by hackers. Finally, become a master of email signatures, and learn how to send giant files that would normally choke a mail server.
Set Your Email to ‘Snooze’ So It Comes Back Later
Here’s how to make messages bubble back to the top of your inbox—on your schedule.
A crowded inbox can be a productivity killer, if for no other reason than that important messages can get pushed out of sight by newer ones. What you need is a kind of “remind me later” button for email, a way to defer selected messages to a later date or time before they drop “below the fold.”
Outlook and Gmail users should check out Baydin’s Boomerang, which lets you reschedule email with just a few clicks. Or, if you’re not a fan of plug-ins, services like Followup.cc and NudgeMail work with any email system: You just forward a message to a specialized address ([email protected], for example, or [email protected]), and you’re done. The email will reappear in your inbox at the designated time and date. And if you’re still not ready to act on the message, just click one of the embedded “snooze” options and go back to sleep—er, work.
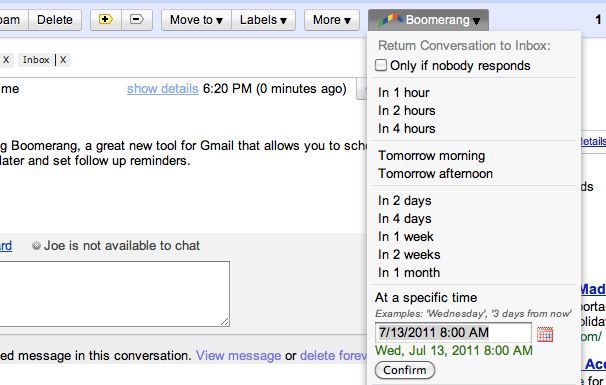 Boomerang for GMail can help keep important messages you can’t read right away from getting buried by newer mail.
Boomerang for GMail can help keep important messages you can’t read right away from getting buried by newer mail.
Both Followup.cc and NudgeMail are free. Boomerang for Outlook costs $30, though you can try it free for 30 days. Boomerang for Gmail offers its Basic plan (ten messages per month) free of charge; you can upgrade to a Personal plan (unlimited messages) for $5 monthly.
Tame Gmail With Priority Inbox and Dethreaded Conversations
GMail Priority InboxPriority Inbox is Gmail’s answer to email overload. By evaluating your reading and replying habits, it predicts which messages are most important and “floats” them to the top of your inbox, corraling the less-important stuff for later viewing. (You can tweak the prediction accuracy by clicking a “plus” or “minus” button for any given email.) It’s kind of like having a personal assistant who separates the email wheat from the email chaff.
To enable Priority Inbox, head to your Gmail settings, click the Inbox tab, and then choose Priority Inbox from the “Inbox type” drop-down menu. Then click Save Changes and return to your inbox.
Alternatively, while you’re in the settings area, consider turning off one of Gmail’s most controversial features: Conversation View, which groups together messages with the same subject line. The longer a message thread gets, and the more people who participate in it, the harder it becomes to find the newest addition—or to review earlier replies. In other words, these “conversations” can quickly turned into muddled, incomprehensible, frustrating messes.
To turn off Conversation View—which will make messages appear one after another (as in most traditional email systems)—click over to the General tab, then set Conversation View to off. Click Save Changes when you’re done.
Protect Your Privacy With Disposable Email Addresses
You know the routine: There’s some new service, promotion, or online freebie that requires your email address–but you don’t want the inevitable deluge of ads, updates, and other inbox spam. How can you sign up without actually sharing your email address?
Mailinator is simple and free to use.What you need is a disposable address, one that won’t negatively impact your inbox. Suppose you’re staring at a registration form and don’t want to use your regular email account. Just make up an address (like “ihatespam”) and tack on @mailinator.com. Then head to the free Mailinatorservice and sign in using the address you just created; you’ll find a Web-accessible inbox you can use to retrieve your promotional code, download link, or whatever. All Mailinator mail gets deleted within a day.
Mailinator isn’t the only disposable-email game in town. Services like 10 Minute Mail, Humaility, and YopMail offer similarly convenient registration-free addresses. And if you’re a Firefox user, Less Spam, Pleaseintegrates with these services, generating a disposable, reusable email address when you right-click in an email field and choose Insert a temporary mail address. Doesn’t get much easier than that.
Instantly Paste Your Choice of Email Signatures
An email signature is a great way to share snippets of contact information: your phone number, Facebook/Twitter addresses, website, and so on. But with most email systems and programs, it’s an all-or-nothing affair: signatures are either “on” or “off,” and you’re limited to just one appended block of text. What if you want to add your signature to some emails but not others? And what if you want to share different contact blurbs with business associates than you do with friends and family?
The solution: an “autotext” or macro program that quickly and automatically turns abbreviated text into expanded blocks of text.
For example, you could create a custom signature that you’ll use only with clients and customers, and designate it “bizsig.” Then, when you’re done composing an email, you just type bizsig at the end. Presto: The autotext program instantly inserts your full business signature.
You could take the same approach for a more generalized signature, designating it “sig1” or the like, then just paste it in as needed. And that’s the beauty of this approach: You apply a signature when you want one and skip it when you don’t.
A number of programs afford this kind of macro-powered convenience; two of the most popular are AutoHotKey and PhraseExpress. Both are free, but the latter is definitely the more user-friendly of the two. (AutoHotKey requires a bit of scripting.)
Find Out If Your Email Account Has Been Hacked
It seems that every day we hear about another email database being compromised by hackers. The “good” news is that these petty thieves often post the stolen databases online. The bad news is, there’s no way to know for sure if your email address has been compromised.
There is now: HackNotifierchecks your email address against the growing number of publicly available “hacked” email databases. Just type in your address and click Have I been hacked? If the results are negative, you can rest easy–though you should continue to be diligent about using strong passwords and varying them from site to site.
Verify that your e-mail account hasn’t been hacked with HackNotifier.
If the news is not good, HackNotifier will tell you which accounts were compromised and provide more information about the leaks. The service also offers 24/7 account monitoring for $5 per year ($7 if you want instant notification via text message). What it doesn’t do is offer any instructions on how to safeguard your email security if an account has been hacked. Check out numerous ways of Creating an effective password
Send Super-Huge File Attachments
As a general rule, mail servers don’t like large file attachments. While some can accommodate files as large as 25MB, others balk if they exceed just 5MB. In these days of mammoth videos, photo libraries, PDFs, and the like, that doesn’t always cut it.
What you need is a file-sharing service that bypasses your mail server. Countless options are available, including such cloud-storage stalwarts as Dropbox and SugarSync(which give you 2GB and 5GB of free space, respectively). You simply upload your file(s) to a public folder, copy the “share” link, and paste that link into an email. The recipients will be able to download the file(s) via the link, effectively taking mail servers out of the equation.
SugarSync is a perennial favorite for storing and sharing files online.
If you’d rather not sign up for yet another service, or you just want a more straightforward way to share your big files, try Ge.tt. In about the time it takes to read this sentence, you can upload a file and get a link to hand out—no registration, software, or plug-ins required. Files remain available for 30 days, or 90 if you elect to sign up for an account (which is free). That account also gives you real-time sharing statistics, something you definitely can’t get from email.
On the other hand, if you prefer the traditional (some would say easier) email-attachment method, file-sharing service YouSendIt offers a free Microsoft Outlook plug-inthat does an end run around your mail server, while still making big-file sharing as simple as creating an attachment. Note, however, that the maximum file size is 50MB unless you sign up for a Pro account ($10 monthly or $50 per year), which raises the maximum to 2GB.
With these tools in your arsenal, it won’t be long before you’re sending and sorting email like a pro.



















 How to make money online:There are so many articles on “How to make money online” and over 1000 get rich quick schemes jobs online which has proven useless and abortive in assisting you in earning online. Before I continue, I want you to know that this is not a get-rich-quick scheme and I am going to tell you why it is not. This article does not promise you any sure means, through which you can make money online doing little or no jobs neither is it an investment program that you go into and sit and home. In a nutshell you have to work hard to make money through the methods you will be seeing below.
How to make money online:There are so many articles on “How to make money online” and over 1000 get rich quick schemes jobs online which has proven useless and abortive in assisting you in earning online. Before I continue, I want you to know that this is not a get-rich-quick scheme and I am going to tell you why it is not. This article does not promise you any sure means, through which you can make money online doing little or no jobs neither is it an investment program that you go into and sit and home. In a nutshell you have to work hard to make money through the methods you will be seeing below.
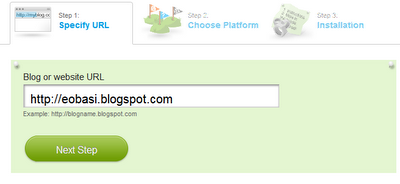
 Tips on Becoming a Successful Blogger: The internet has been one of the widest sources of knowledge and income, and blogging is one of the ways to make some good cash. There are over 10 million blogs and this number increases every day. Blogging is very good and interesting, especially when you are not going into it because of the money you could make. It allows you to share your opinion with the world at large and also reach out to people in need of help and advice. Some people will just rush into blogging without knowing what it involves. You must read this article and know why you shouldn’t start blogging. Here are some facts about blogging you should know and have in mind Tips on becoming a successful blogger
Tips on Becoming a Successful Blogger: The internet has been one of the widest sources of knowledge and income, and blogging is one of the ways to make some good cash. There are over 10 million blogs and this number increases every day. Blogging is very good and interesting, especially when you are not going into it because of the money you could make. It allows you to share your opinion with the world at large and also reach out to people in need of help and advice. Some people will just rush into blogging without knowing what it involves. You must read this article and know why you shouldn’t start blogging. Here are some facts about blogging you should know and have in mind Tips on becoming a successful blogger










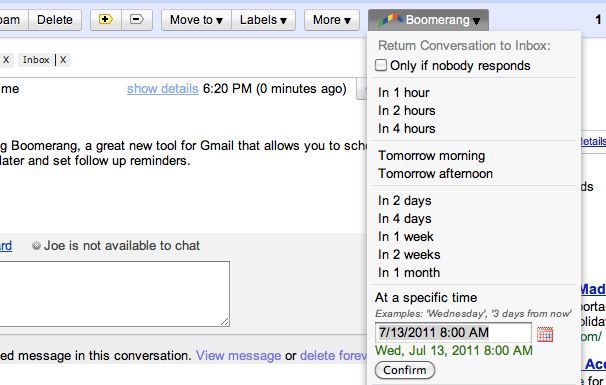 Boomerang for GMail can help keep important messages you can’t read right away from getting buried by newer mail.
Boomerang for GMail can help keep important messages you can’t read right away from getting buried by newer mail.
